Language Learning Models (LLMs) represent a cutting-edge advancement in artificial intelligence, offering capabilities that extend far beyond traditional security measures. LLMs are designed to understand and generate human-like text, analyzing vast amounts of data to identify patterns and context. This ability makes them incredibly versatile, with applications ranging from customer service to content generation and, critically, enhancing security strategies.
The significance of LLMs in security lies in their capacity to process and interpret large datasets quickly, enabling businesses to detect and respond to threats more effectively. By leveraging LLMs, companies can develop advanced security strategies that not only address current threats but also anticipate future risks.
How AI is Learning Human Language
Language Learning Models (LLMs) are a subset of artificial intelligence designed to understand, generate, and manipulate human language. They leverage advanced algorithms and vast datasets to predict and generate text that is contextually relevant and coherent.
Examples of prominent LLMs include OpenAI’s GPT-4, Google’s BERT, and Facebook’s RoBERTa. These models have demonstrated remarkable proficiency in tasks such as language translation, text summarization, and conversational AI.
How LLMs Work
LLMs operate through a process known as deep learning, which involves training neural networks on large text corpora. This training enables the models to learn the nuances of language, including syntax, semantics, and context. The models are designed to predict the likelihood of a word or phrase occurring in a given context, which allows them to generate text that is both relevant and coherent.
The architecture of LLMs typically includes layers of transformers, which are responsible for processing and analyzing the input data in parallel, making the models highly efficient and effective in understanding complex language patterns.
Current Applications of LLMs in Various Industries
- Customer Service
Automated chatbots powered by LLMs provide instant and accurate responses to customer inquiries, enhancing customer satisfaction and operational efficiency. - Healthcare
In the healthcare sector, LLMs assist in diagnosing diseases by analyzing medical records and research papers, offering support for medical professionals. - Finance
Financial institutions use LLMs to detect fraudulent activities by monitoring transaction patterns and identifying anomalies in real-time. - Marketing
LLMs help marketers create personalized content by analyzing consumer behaviour and preferences, leading to more targeted and effective campaigns. - Education
Educational platforms leverage LLMs to develop intelligent tutoring systems that provide personalized learning experiences and instant feedback to students.
How LLMs Identify and Mitigate Security Threats
Language Learning Models (LLMs) possess the capability to analyze large volumes of data and identify patterns indicative of security threats. By processing network traffic, user behaviour, and other relevant data, LLMs can detect anomalies that may signal potential breaches.
They are adept at recognizing unusual patterns, such as irregular login attempts or data access patterns, and can trigger alerts for further investigation. Additionally, LLMs can automate the analysis of threat intelligence reports, helping security teams stay ahead of emerging threats.
Examples of Security Issues Addressed by LLMs
LLMs have proven to be effective tools in addressing various security challenges faced by businesses. These advanced models analyze vast amounts of data to identify and mitigate threats in real-time. By leveraging their deep understanding of language patterns and behaviours, LLMs can accurately detect and respond to anomalies that may indicate security breaches.
Their ability to adapt and learn from new data allows them to stay ahead of emerging threats, providing robust protection for sensitive information and systems. From identifying phishing attempts to preventing fraudulent activities and detecting malware, LLMs are an integral part of modern security strategies, ensuring businesses can operate securely in an increasingly digital landscape:
- Phishing Detection
LLMs analyze email content to identify phishing attempts, flagging suspicious emails based on language patterns and context. - Fraud Prevention
Financial institutions use LLMs to monitor transactions for signs of fraud, such as unusual spending patterns or large, unexpected transfers. - Malware Detection
By analyzing code and behaviour patterns, LLMs can identify malware and other malicious software before it causes significant damage. - Insider Threats
LLMs monitor employee behaviour and communication to detect potential insider threats, ensuring that sensitive information remains secure.
Benefits of Using LLMs in Security Strategies
The proactive capabilities of LLMs allow businesses to anticipate and prepare for emerging threats, ensuring a robust and adaptive security posture. By automating routine security tasks, LLMs free up valuable resources, allowing security teams to focus on more complex and strategic issues.
These benefits collectively make LLMs a vital component of contemporary security strategies, helping organizations maintain a strong defense against ever-evolving cyber threats:
- Enhanced Accuracy
LLMs improve the accuracy of threat detection by reducing false positives and focusing on genuine threats. - Real-Time Analysis
The ability of LLMs to process and analyze data in real-time enables quicker response times, mitigating the impact of security breaches. - Scalability
LLMs can handle vast amounts of data, making them suitable for large organizations with extensive networks and data flows. - Proactive Threat Management
By continuously learning from new data, LLMs can anticipate and adapt to emerging threats, providing a proactive approach to security. - Resource Optimization
Automating routine security tasks with LLMs allows security teams to focus on more complex issues, optimizing the use of human resources.
Implementing LLMs for Enhanced Security Strategies
Integrating Language Learning Models (LLMs) into your existing security framework involves several critical steps:
-
Assessment
Begin by assessing your current security infrastructure to identify areas where LLMs can provide the most benefit. This includes evaluating the types of data you collect, the threats you face, and your existing detection and response capabilities. -
Selection of LLM Tools
Choose the appropriate LLM tools that align with your security needs. Consider factors such as model accuracy, scalability, ease of integration, and cost. -
Data Preparation
Prepare your data for LLM integration. This involves cleaning and organizing your data to ensure that the LLMs can effectively analyze and learn from it. Ensure that sensitive information is anonymized or encrypted to maintain privacy. -
Integration
Seamlessly incorporate LLMs into your security systems. This may involve working with experienced developers to ensure that the integration is smooth and that the LLMs can effectively interact with your existing infrastructure. -
Training and Fine-Tuning
Continuously train and fine-tune the LLMs using your data to ensure they remain effective. This includes updating the models with new data and refining their algorithms to improve accuracy. -
Monitoring and Evaluation
Regularly monitor the performance of the LLMs and evaluate their effectiveness in identifying and mitigating security threats. Adjust your strategies as needed to optimize performance.
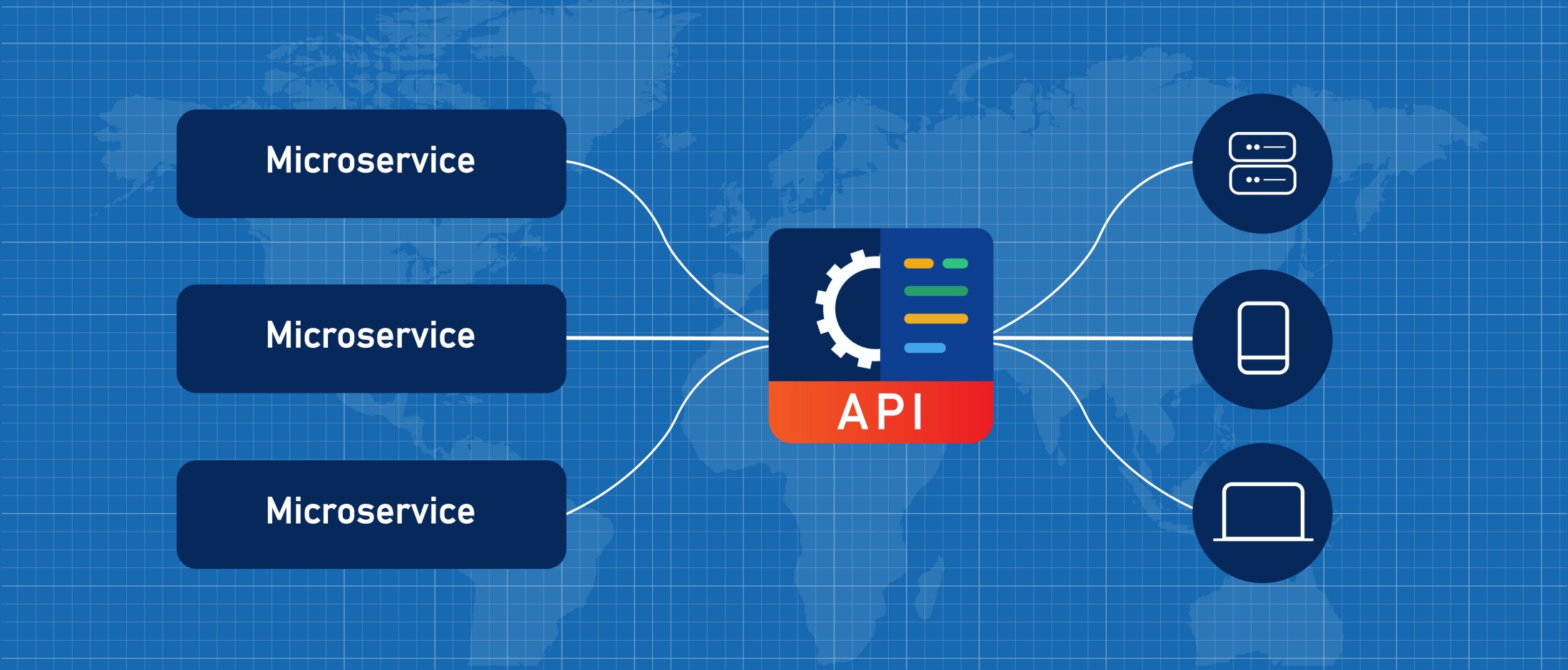
Tools and Platforms That Support LLM Integration
These resources provide the necessary infrastructure, pre-trained models, and development frameworks that simplify the implementation process. They offer user-friendly interfaces and robust APIs, enabling seamless integration with existing security systems.
The availability of scalable solutions ensures that companies can grow their security capabilities in line with their evolving requirements, ultimately fostering a more secure and resilient digital environment:
-
OpenAI
Offers powerful LLMs like GPT-4 that can be customized for various security applications. OpenAI provides APIs that make it easier to integrate their models into your systems. -
Google Cloud AI
Provides robust AI and machine learning services, including pre-trained models and tools for building custom LLMs. Google Cloud’s platform is highly scalable and suitable for large organizations. -
Microsoft Azure AI
Azure offers a comprehensive suite of AI tools, including language models that can be integrated into security systems. Azure’s platform supports various programming languages and frameworks, making it versatile for different applications. -
Hugging Face
An open-source platform that provides access to a wide range of pre-trained LLMs and tools for fine-tuning and deploying models. Hugging Face is known for its user-friendly interface and extensive model library.
Best Practices for Implementing LLMs
To ensure the successful implementation of LLMs in your security strategies, follow these best practices:
-
Start Small
Begin with a pilot project to test the integration of LLMs into your security systems. This allows you to identify potential issues and make adjustments before scaling up. -
Collaborate with Experts
Work with AI and security experts to ensure that the integration is seamless and that the LLMs are optimized for your specific needs. -
Continuous Learning
LLMs should be continuously trained with new data to stay effective. Regularly update your models to keep up with emerging threats and changes in data patterns. -
Data Privacy
Ensure that data privacy and ethical considerations are prioritized. Anonymize sensitive data and comply with relevant regulations to maintain trust and integrity. -
Performance Monitoring
Implement robust monitoring and evaluation processes to track the performance of LLMs. Use metrics such as detection accuracy, false positive rates, and response times to gauge effectiveness. -
Scalability
Design your LLM integration to be scalable, allowing you to expand the use of LLMs as your needs grow. This ensures that your security strategies can adapt to increasing data volumes and evolving threats.
Overcoming Challenges and Ethical Considerations
Integrating LLMs into security strategies comes with its set of challenges and ethical considerations. The complexity of implementation, high costs, and the need for high-quality data are significant hurdles that organizations must navigate. Additionally, ensuring data privacy and addressing potential biases in the models are critical ethical issues that need careful management.
Despite these challenges, businesses can effectively leverage LLMs by adopting strategic approaches to mitigate risks and prioritize ethical practices. This involves thorough planning, collaboration with experts, continuous monitoring, and adherence to privacy regulations.
Potential Challenges in Using LLMs for Security Strategies
Implementing Language Learning Models (LLMs) in security strategies comes with several challenges:
- Complexity of Integration
Integrating LLMs into existing security frameworks can be complex and resource-intensive. It requires a deep understanding of both the technology and the specific security needs of the organization. - High Costs
The initial investment in LLM technology, including purchasing, integrating, and maintaining these models, can be substantial. This includes not only financial costs but also the time and effort required for implementation. - Data Quality
The effectiveness of LLMs is highly dependent on the quality of the data they are trained on. Poor-quality data can lead to inaccurate predictions and ineffective security measures. - Scalability Issues
As the volume of data grows, scaling LLMs to maintain performance and efficiency can be challenging. This requires robust infrastructure and continuous monitoring.
Ethical Considerations and Data Privacy Concerns
Using LLMs for security involves several ethical and data privacy considerations:
- Data Privacy
LLMs require access to large datasets, which may include sensitive or personal information. Ensuring that this data is handled in compliance with privacy regulations (such as GDPR or CCPA) is crucial. - Bias and Fairness
LLMs can inherit biases present in the training data, leading to unfair or discriminatory outcomes. It’s essential to ensure that the models are trained on diverse and representative datasets. - Transparency and Accountability
The decision-making processes of LLMs can be opaque, making it difficult to understand how certain conclusions are reached. Ensuring transparency and accountability in the use of these models is critical. - Security Risks
Paradoxically, the use of LLMs can introduce new security risks, such as adversarial attacks where malicious actors manipulate the input data to deceive the model.
How to Address and Mitigate These Challenges
To effectively address and mitigate the challenges and ethical considerations associated with using LLMs in security strategies, consider the following approaches:
- Thorough Planning and Assessment
Conduct a comprehensive assessment of your current security framework and identify specific areas where LLMs can provide the most value. Plan the integration process carefully to manage complexity and costs. - Invest in High-Quality Data
Ensure that the data used to train LLMs is of high quality, relevant, and free from biases. Regularly update and clean your data to maintain the accuracy and reliability of the models. - Robust Privacy Measures
Implement strong data privacy practices, including data anonymization, encryption, and access controls. Ensure compliance with all relevant regulations and industry standards. - Bias Mitigation
Actively work to identify and mitigate biases in your training data. Use techniques such as data augmentation and fairness-aware training to promote fairness and equity in model outcomes. - Enhance Transparency
Increase the transparency of your LLMs by documenting the decision-making processes and providing clear explanations for their outputs. Implement mechanisms for accountability and regular audits. - Strengthen Security Measures
Address potential security risks by regularly testing the robustness of your LLMs against adversarial attacks. Employ techniques such as adversarial training to improve resilience. - Continuous Monitoring and Evaluation
Establish a robust monitoring system to continuously evaluate the performance of your LLMs. Use metrics such as accuracy, bias, and response times to identify areas for improvement and ensure ongoing effectiveness.
Emerging Trends and Advancements in LLM Technology
LLMs are undergoing rapid transformation, with innovative trends and technological advancements poised to significantly enhance security strategies. As these trends continue to evolve, they promise to provide businesses with more powerful tools to stay ahead of emerging cyber threats and maintain robust security postures:
- Improved Model Architectures
New architectures, such as transformers, are making LLMs more efficient and effective. These advancements allow for better handling of context and more accurate predictions, enhancing their utility in security applications. - Federated Learning
This technique enables models to be trained on decentralized data sources without compromising privacy. Federated learning allows LLMs to improve security measures while maintaining compliance with data privacy regulations. - Real-Time Processing
Advancements in hardware and software are enabling real-time data processing, allowing LLMs to analyze and respond to security threats instantly. This capability is crucial for mitigating threats as they occur. - Integration with Other AI Technologies
Combining LLMs with other AI technologies, such as computer vision and anomaly detection algorithms, creates more comprehensive and robust security systems. This integration enhances the overall effectiveness of security strategies. - Explainable AI (XAI)
Developing models that provide transparent and understandable explanations for their decisions is a growing trend. XAI helps build trust in LLM-based security systems by making their decision-making processes more transparent.
Predictions for Future Applications in Security Strategies
Looking ahead, the application of LLMs in security strategies is poised to expand significantly:
- Proactive Threat Hunting
LLMs will increasingly be used to predict and identify potential threats before they manifest. By analyzing patterns and trends, these models can anticipate and neutralize threats proactively. - Automated Incident Response
Future LLMs will play a role in automating incident response, reducing the time taken to address security breaches. They will be capable of autonomously executing predefined response plans, mitigating damage swiftly. - Enhanced Cyber Defense
LLMs will be integrated into broader cyber defense frameworks, providing real-time insights and actionable intelligence. This integration will enhance the overall resilience of organizations against sophisticated cyber attacks. - Adaptive Security Systems
The ability of LLMs to learn and adapt continuously will lead to the development of dynamic security systems. These systems will evolve in real-time, adapting to new threats and vulnerabilities as they emerge. - Human-AI Collaboration
The future will see more seamless collaboration between human security experts and AI models. LLMs will provide actionable insights and recommendations, enabling security professionals to make more informed decisions and focus on complex tasks.
Strengthening Security Strategies with Technology
Leveraging LLMs is essential for developing advanced and resilient security strategies. The unique capabilities of LLMs—such as real-time threat detection, automated incident response, and predictive analytics—make them invaluable tools for safeguarding digital assets against sophisticated cyber threats.
By integrating LLMs into their security frameworks, businesses can significantly enhance their ability to protect sensitive information, anticipate potential risks, and respond to incidents swiftly and effectively.
For businesses seeking to enhance their security strategies through the implementation of LLMs, partnering with experts is crucial. At e-dimensionz Inc., our experienced team is ready to help you navigate the complexities of integrating LLMs into your security framework. Contact us for a consultation on how we can assist you in leveraging LLMs to achieve advanced security solutions tailored to your specific needs.